DMARC is not the be-all/end-all solution of email deliverability issues, and it is not for everyone. DMARC is only a concern for domains that are trying to eventually move to a “reject policy”, and for organizations who care about their domain’s branding being used without permission.
What is DMARC?
DMARC, which stands for “Domain-based Message Authentication, Reporting & Conformance” is a technology that aims to prevent spoofing of from addresses. DMARC helps to authenticate emails via SPF and DKIM mechanisms. When DMARC is in place, small to large businesses are fighting email phishing, spoofing and compromise.
What is a DMARC Record?
DMARC records act as a safeguard check ISPs will use to prevent email spoofing or phishing. The DMARC records check, helps to validate email senders. It helps email senders figure out how to deal with emails that didn’t get authenticated by dkim or spf. Email senders can choose to force all emails that didn’t get authenticated to the junk folder or can ignore them completely.
How to setup DMARC?
Implementing DMARC does not immediately help improve inbox placement rates. In fact, it could limit inbox placement because email authentication protocols can be rather sensitive in determining what gets through versus what doesn’t. Having a DMARC “reject” policy can amplify such sensitivities, limiting the amount to email coming through that do not pass SPF or DKIM. However, in the longer term, a DMARC policy provides protection from malicious entities who are trying to leech your reputation. By setting up and enforcing strict DMARC policies, you can help mailbox providers “authenticate” the emails you send which will indirectly help improve inbox placement over time by strengthening a sender’s reputation.
Implementing a DMARC Policy for Your Domain
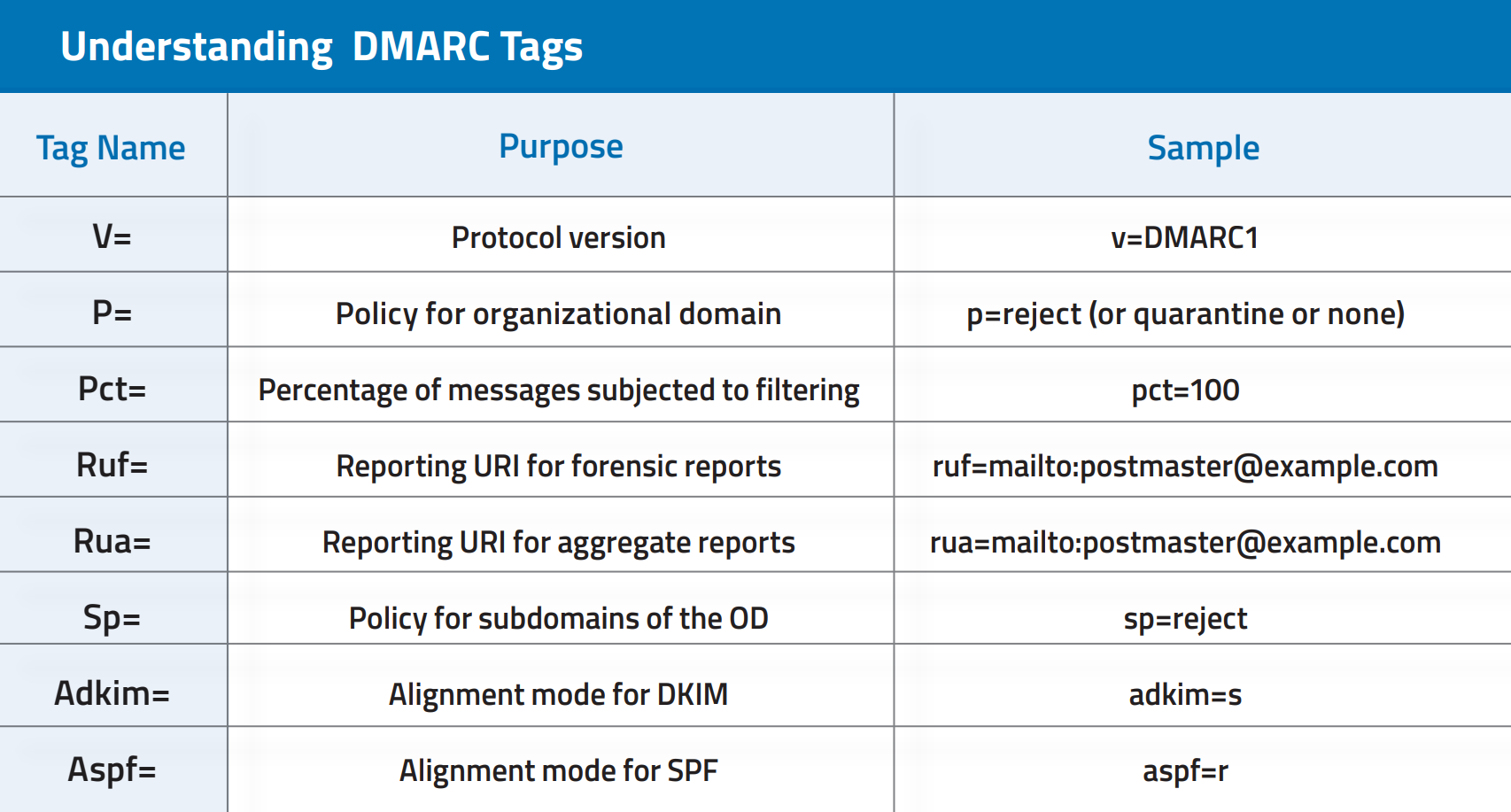
Below is an example of a DMARC record that you would want to configure in your domain’s DNS records. There are a variety of tags used in your DMARC record, but only the “version” tag (v=) and the “policy” tag (p=) are required for DMARC to be configured correctly. Currently, there is only one version of DMARC. The version tag was created for the future of DMARC. “v=DMARC1; p=reject; pct=100; rua=mailto:[email protected]”
The process of implementing DMARC does not need to be implemented all at once, rather it can be done in stages. Your first step is going to be setting up a mailbox to receive your aggregate DMARC reports.
Why does DMARC Fail?
DMARC.org suggests that a domain owner set the DMARC policy tag (p=) to “none” as a means to begin collecting data. Doing so is known as setting DMARC to “monitor mode.” There are many tools available to a domain owner to view the collected data. The three most popular tools for DMARC belong to Dmarcian, Agari, and 250ok. SocketLabs currently has a “none” policy, and has been using Dmarcian’s tools to monitor and adjust our domain’s DMARC compliance before we move to a “reject” policy.
Once the data collected for your domain confirms that your legitimate traffic is passing authentication checks, you can change your policy to request that failing messages be quarantined. By setting your DMARC policy to “quarantine,” you are instructing mail servers to put messages using your domain that fail DMARC checks into a location on the receiving email infrastructure and to send a report back to the RUA or RUF address specified in your policy. How exactly a message is quarantined is specified by the recipient system. Typical examples of quarantine are delivering the failed messages to spam folders or holding messages in a database for further investigation by an email administrator.
Once you are confident that legitimate messages are not failing DMARC and being quarantined, you can change your policy to “reject.”
Within the DMARC policy you can also control the granularity of messages that are subject to the policy. The “pct” flag denotes the percentage of messages that should be evaluated. The balance (those not being evaluated) are subjected to the next less-restrictive policy. For example, if you were to set your DMARC policy to “reject” and have “pct” set to “50,” half of your messages would be rejected, and the other half would be quarantined. If you set the DMARC policy to “quarantine” and have the “pct” set to “50”, half of your messages would be quarantined, and the other half would just process through without issue. The “pct” flag does not apply to monitor mode because “none” is the least restrictive of the modes available.
What is a DMARC Failure?
A dmarc failure is when both the spf verification and the dkim verification tests fail. When this happens, email deliverability can be affected, since inboxes cannot verify the authenticity of the email.
Do you need DKIM for DMARC?
No you don’t, you can just use DMARC and SPF, but this is a less than ideal setup to use. As SPF records don’t carry on the same information dkim records do, so you can run into issues where emails will be marked as spam, in these cases, dkim setup may be needed.
SocketLabs has created Free Email Tools to help developers and email administrators generate a valid DMARC policy for your domain.